By far the oldest and most consistent requirement in the PCI-DSS is requirement 8 and specific password controls.
The Visa CISP standard which is the forerunner to PCI version 1.0 (pre-2006) included these same password requirements which can be found in the current version 3.2.1 and summarized as follows:
- Passwords must meet a minimum length of at least 7 characters.
- Passwords must include both numeric and alphabetic characters.
- Passwords must be changed every 90 days.
- Individuals may not set or reuse a password that is the same as any of the last 4 passwords he or she has used.
- Passwords must be encrypted when transmitted or stored.
These requirements were based on NIST password standards and generally accepted throughout the then nascent cybersecurity industry. The industry was generally shocked following a series of articles in the summer of 2017, which stated that Bill Burr, an author of NIST password guidelines in 2003, had essentially recanted all prior guidance in line with a NIST update. Numerous password breaches between 2000 and 2015 had provided researchers with hard data and demonstrated that the stated password requirements within NIST and adopted within the PCI-DSS, made passwords more difficult to remember, and easier for computers to crack. This concept is encapsulated in the XKCD classic comic “Password Strength”.
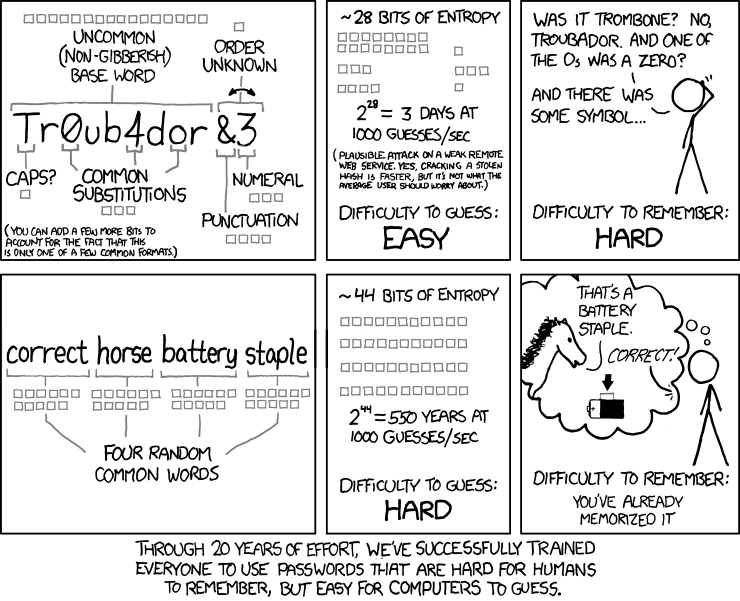
Figure 1: xkcd Comic: Password Strength - xkcd.com/936/
Shortly after these revelations came to light, clients began asking Intersec assessors how PCI-DSS standards would be impacted by these changes and if they could implement longer passwords and remove the 90-day password change requirement. These inquiries were promptly sent to the PCI Security Standard Council (PCI-SSC) who in August 2019 released an FAQ (1467) stating that alternative password requirements could be used provided all NIST guidelines were followed, and a compensating control sheet was completed.
NIST guidelines essentially stated the following regarding memorized secrets (passwords):
- Passwords must meet a minimum length of 8 without any enforcement of complexity
- Passwords should only be changed if they are suspected to be compromised or appear in previous password breach.
- Candidate passwords submitted by users should be evaluated for the following:
a. Reject if the password is present in previous password breach disclosure
b. Dictionary words
c. Repetitive characters such as (‘aaaaaaa’ or ‘1234abcd’)
d. Context specific – such as the name of a company, service or username
Most clients were on board and could easily implement requirement 1. However, addressing requirements 2 and 3 were more difficult. While gigabytes of compromised passwords were available for free, implementing a process to check these lists was not readily available at the time. Since then, a few vendors have stepped up and provided password management services to meet requirements 2 and 3.
PCI-DSS 4.0 Password Requirement Changes
The council has obviously acknowledged updated NIST guidance in the new PCI-DSS 4.0 version. According to requirement 8.3.6, passwords must be increased in length from 7 to 12 characters with an exception for legacy systems that only support 8 characters. Passwords must still contain numeric digits and alphabetic characters. Requirement 8.3.7 still requires organizations to ensure the last 4 passwords cannot be reused.
Perhaps the most significant change is stated in requirement 8.3.9, which still requires passwords to change every 90 days if only a password is used (w/o MFA) OR an organization may forgo enforcing password changes if accounts are dynamically analyzed and real-time access to resources is automatically determined. In other words, organizations that have enabled Zero-Trust and behavioral user analytics can enforce password changes based on perceived risk or compromise.
It should be noted that requirement 8.3.10 extends requirement 8.3.9 to service provider’s customers. This was not explicitly stated in version 3.2.1.
Requirements 8.6.2 and 8.6.3 in version 4.0 also impact password requirements specifically for application and system accounts. These accounts were not explicitly covered in version 3.2.1 of the standard, which left the password complexity and change frequency up to a QSA’s discretion. Changing a system account every 90 days is difficult for most organizations and creates a significant risk for a system outage.
Starting on April 1, 2025, organizations will need to perform a targeted risk analysis to determine password length and change frequencies and then implement processes to ensure passwords are changed.
At a minimum passwords for application accounts will need to meet the 12-character length standard with 15 characters being stated as a “good practice”.
Intersec Password Recommendations to Clients
Given that stolen user credentials are involved in close to 40% of data breaches1, Intersec has always believed the version 3.2.1 password standard of 7 characters was too low and easily cracked through brute force using today’s graphics processing units (GPU).
Per updated NIST guidance, Intersec encourages clients to use 12-character length passwords for general accounts and 16-character passwords with multi-factor authentication (MFA) for administrative accounts.
How can you use privileged access to enhance security?
Intersec strongly recommends (although not required by PCI-DSS) that users with privileged access be granted two (2) separate accounts. One account is used for daily activities like initial network login and checking e-mail. A separate privileged account is used for system and server administration with greater controls placed on these accounts such as MFA and passwords with greater length attributes. A privileged session manager such as Thycotic and CyberArk can help exceed these standards by automatically changing privileged passwords at a set interval, such as every 8 hours.
We strongly recommend passwords for these accounts be set with up to 25+ alphanumeric characters. This solves two goals. First, the length of the password ensures it is virtually impervious to brute force attacks. Second, and probably most important, the length and complexity of the password will likely deter administrators from wanting to use the password out of convenience.
How often should email passwords and passwords for service accounts be changed, and what are the recommended practices for these changes?
Intersec has also always enforced password changes for service accounts, typically every 12 to 18 months. PCI DSS 4.0 advocates for a more flexible approach to password changes for service accounts, suggesting changes be based on risk assessments rather than adhering strictly to a predefined schedule.
Recommended practices include using strong, unique passwords and changing them when indicators of potential compromise are detected. Organizations should employ automated tools to manage service account credentials securely and ensure that changes are made in a controlled manner consistent with their risk management strategy.
If you are planning to update your organization’s password requirements, contact our team today to learn how we can help ensure PCI DSS 4.0 compliance.
[1] Verizon Data Breach Report
PCI 4.0 Transition Plan
The QSAs of Intersec Worldwide have analyzed the PCI-DSS 4.0 standard to identify transitional impacts to our clients’ compliance programs as they migrate to the new version.
We've been working diligently with our clients to get them started on the path to success, and now we want to share our expertise and implementation plan with you!
Our PCI DSS 4.0 Implementation Guide offers detailed insights, including 26 critical priorities every organization should act on. Read, share, and download a PDF of the contents to get started today!
Delays in implementation and understanding will likely lead to missed compliance dates due to failures to meet compliance objectives. Let us help you with our free transition plan and implementation guide.
References:
The Man Who Wrote Those Password Rules Has. New Tip: N3v$rM1-d!
The Wall Street Journal – Aug 7, 2017
https://www.wsj.com/articles/the-man-who-wrote-those-password-rules-has-a-new-tip-n3v-r-m1-d-1502124118
Practical Recommendations for Stronger, More Usable Passwords Combining Minimum-Strength, Minimum-Length and Blocklist Requirements – Carnegie Mellon University – November 9, 2020
https://www.andrew.cmu.edu/user/nicolasc/publications/Tan-CCS20.pdf
NIST Special Publication 800-63B – Digital Identity Guidelines – June 2017
https://pages.nist.gov/800-63-3/sp800-63b.html
Correct Horse Battery Staple Comic (Password Strength)
https://xkcd.com/936/
Can organizations use alternative password management methods to meet PCI-DSS Requirement 8?
PCI-DSS FAQ – 1467 – May 2019
https://www.pcisecuritystandards.org/faq/articles/Frequently_Asked_Question/Can-organizations-use-alternative-password-management-methods-to-meet-PCI-DSS-Requirement-8/
Verizon 2022 Data Breach Investigations Report
https://www.verizon.com/business/resources/reports/dbir/?cmp=knc:ggl:ac:wls:dpr:8888855284&utm_term=verizon%20breach%20report&utm_medium=cpc&utm_source=google&utm_campaign=GGL_BND_Security_Exact&utm_content=DBIR2022&ds_cid=71700000082347933&ds_cid=71700000082347933&ds_cid=&gclid=Cj0KCQjw7KqZBhCBARIsAI-fTKKPB0XJF1LsdWuz86TaaSg-jKGRX9aL9LGHiFCMmEULkpz6A5c2M8caAvYfEALw_wcB&gclsrc=aw.ds
The Nvidia RTX 3090 can probably crack your passwords – October 15, 2020
https://www.extremetech.com/extreme/316266-the-nvidia-rtx-3090-gpu-can-probably-crack-your-passwords